Sailpoint Training | Sailpoint Course for Beginners
How beneficial can SailPoint Training be?
As we know, SailPoint is a crucial IAM tool. It will be worthwhile to have a keen understanding of IAM before taking the SailPoint course.
Identity Access Management (IAM) is crucial for managing access to confidential data and sensitive information. It is essential for organizations with different users, such as employees, contractors, and suppliers, to ensure proper Access control.
An IAM solution can address issues by providing a proper system for managing data, ensuring data sync, and addressing the need for audits and compliance. This is particularly important for organizations with different types of users.
Additionally, IAM can help address the issue of orphan accounts, where accounts are created without real users in the organization.
Now that we have a proper understanding before starting Learning SailPoint let us glimpse this tremendous technology.

SailPoint Tool is one of the top AI-driven security platforms…
This technology offers organizations a comprehensive solution to improve regulatory compliance. This solution includes Federated identity management, access management, and privilege access management.
The company initially launched AI-driven, but now they offer extended management under lifecycle management, compliance management, and extended access management.
This technology provides four products:
• Identity Management
• Security IQ
• File Access Manager
• Identity IQ
Get the SailPoint Tutorial and learn about identity governance.
It is a flexible tool that allows customization and addresses various organisational issues. Join SailPoint Training to learn how this tool offers flexibility in terms of customization.
For example, if a company needs to change an approval policy or onboard a new application, the process can be automated through provisioning and joiner processes.
In this technology, you will learn how it provides a minimum default access for users, such as IT department employees, and allows them to request additional access through the access request tool. Once approved, they receive the necessary access.
However, SailPoint Training Online also helps you understand that how it automates some default actions, such as adding a Windows Active Directory account for new users when they join the organization.
When a user leaves the organization, this software automatically restricts access, as the manager only leaves that day. Only authorized users can access the system without manipulating data or writing. To find more interesting features, get SailPoint Free Training.
SailPoint Identitynow Training explains this IAM software.
So, a process is required for installing SailPoint software. To learn about those steps, see the SailPoint University Training. Installing it requires several steps, including installing the Java Virtual Machine, installing the SQL server and workbench, and selecting the appropriate version of the SQL product.
There are instructions on updating Java JDK and SQL parts in a system using a Notepad file. The instructions emphasize the importance of being cautious when adding or removing parts, as errors may occur.
This helps firms adopt and operate this software, improving efficiency and security.
Next, we need to follow a step-by-step guide process for deploying software and creating a database for an application server. To access the IAQ console, import the necessary files and identity to log into this software.
Security measures are also covered in SailPoint Course Online.
Is SailPoint Identitynow Training implementing these days by organizations in order to enhance employee access and security on non-education systems? The next crucial aspect we will learn from this training is Application onboarding.
Application onboarding is a crucial aspect of this technology, a platform used for managing identities and their access. It involves creating an application to import all the identities who have already access to the application, which can be managed efficiently.

Connectors are pieces of code that act as bridges between the application and the internal database. They work as mediators between this software and the target application, allowing for retrieving application details and identities.
For example, if application data is stored in a database, cloud application, or free file, like a spreadsheet, it can be retrieved from the database. Professionals in the IT sector received comprehensive instruction on identity governance and access management through the SailPoint Full Course.
SailPoint Basic Training will enhance your skills.
SailPoint Training Course will also teach you about other aspects. Password management is another important aspect of creating an application. This program requires a minimum character length, maximum character number, upper and lower case, and a minimum history length.
You can use an IAM tool like Active Directory or GPOs to create a password policy. You can define your Authentication policies as per client requirements, including minimum characters, maximum number of characters, digits, upper and lower case, and special character password history length.
The default password policy has been created in the back end, and you can use it for existing ones by adding the existing policy. The password must have at least four digits and cannot reuse any of the last eight passwords.
Users can submit access requests by logging in to the system, clicking on the “access” icon, and then submitting the request for application access, entitlement, or roles. Once approved, the request goes for provision.
The process of submitting an access request involves approval, which can be configured through the LCM page. Once approved, users can define four levels of approval: manager, entertainment owner, role owner, or application owner.
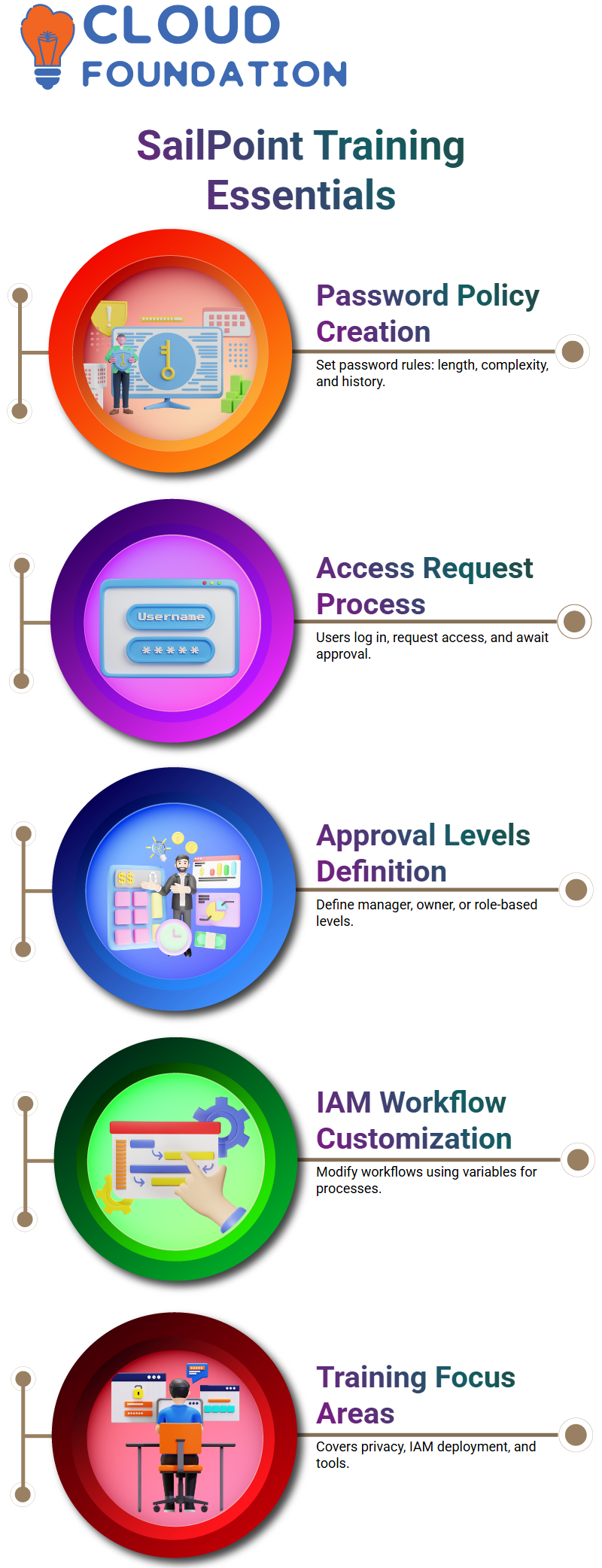
SailPoint Technologies training teaches data privacy.
Enroll in SailPoint tool training to gain the skills required for a new profession in cybersecurity. Some of it’s tools like SunOcta and IDM focus on approval levels.
Approval levels can be defined using variables such as managers, supervisors, or individuals.
The first level is usually a manager, while the second level is for access, such as entitlement roles or application owners.
In this technology, it is easy to define approval levels using variables. For example, an LCM provisioning workflow can be accessed from the business process, which is the same as the workflow object.
Users can access the workflow from the user interface or the backend object browser to make changes to the workflow using variables to make changes to it using variables. The SailPoint IAM tutorial offers extensive instructions on deploying identity and access management in various businesses.
SailPoint IIQ Online Training
It allows users to create entitlements and roles, but customization options and loopback connectors are available for other capabilities.
This application simplifies processes by combining entitlements, creating roles, and combining them. They simplify the creation and approval of work items and approvals, making managing user access easier.
Roles are objects, and every functionality name is considered an object. Entitlements are managed attributes, and users can search for them using ID or attribute values from the object browser page.
The SailPoint Tutorial for Beginners offers extensive instruction on properly utilizing the platform to administer identities for a secure access and efficiently and efficiently.
Sailpoint Training

IdentityIQ training to learn out-of-the-box workflows…
Roles can be bundled, combining any entitlement to encapsulate other entitlements. Access requests are identified as identity requests, not access requests. The provisioning plan will be used to add access to the user.
These are out-of-the-box workflows, and understanding these workflows is crucial for successful provisioning. SailPoint IdentityIQ Training gives users the ability to configure, administer, and maintain their organization’s identity and access management solution.
Permitted roles are optional and can be obtained through an access request. Users can select and submit roles they require, while required roles are part of the assigned business role and are added to the end user.
Permitted roles are optional and require users to select and submit them through an access request. Understanding these distinctions is crucial for effective role management.
The use of this application on workflows, including LCM provisioning and entitlement creation. They mention that this technology provides a set of workflows for access requests by default, with five sub-workflows.
If the client is not satisfied with the out-of-the-box feature, they can create a new workflow or modify existing ones. Get SailPoint Training Videos and SailPoint Identityiq Training Videos to learn more about Identityiq properly
SailPoint Identityiq Tutorial explains standard attributes
Identity attributes are standard attributes that come with defaults, such as username, bus name, last name, and email manager type.
Extended attributes, or custom attributes, are created to store employee details, such as higher date, location, department, ID, cost, and enter ID. These attributes can be added to the database table to store value.
To create new entitlements from the back end and from the debug page, users can use the managed attribute object.
To create a new entitlement, users can copy and paste the existing entitlement details, remove ID values, and change the display name. For instance, to create a domain user for a bank, users can create a new entitlement with the name “domain users” for the bank.
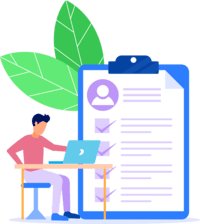
SailPoint Identity Management Training to learn identity mapping
The application attribute uses an identity mapping system to create. The attribute name must be updated in the Hibernate file, altering the table and creating the column index. The attribute should also be added from global settings.
The path to the application attribute is located in the classes folder of Tomcat. The application team may need to add additional attributes for specific roles, such as app custodian, business code, and assignment group.
The complete SailPoint Identity and Access Management Training prepares users to implement and manage the solution in enterprise settings.
Identitynow Training to know about risk management in SailPoint
Risk management is a crucial aspect of corporate security, helping to avoid data breaches and other potential risks. It involves identifying and evaluating risks to minimize their impact.
In this, risk scores can be assigned for each asset, such as identity, resource, application, permissions, and entitlements. These scores help identify the security value of objects, such as roles, entitlement policies, or accounts.
In SailPoint Online Training, you will learn about two types of risks:
• Identity risk
• Application risk
Identity risk is used in real-time projects, where it is difficult to certification for every entitlement and user at the moment. By assigning a risk score, users can easily validate their entitlements and filter out those with high-risk scores.
To assign a risk, go to the Identity Risk Model and click on the baseline access risk or composite risk. Baseline access risk provides a risk point based on the high risk associated with privilege entitlement or privileged access management. High risk points can be assigned to roles, rules, or entitlements.
The Qualitative SailPoint Identityiq Online Training
the organization’s ability to administer user identities and access rights has been substantially enhanced through the implementation of SailPoint IdentityIQ training, resulting in improved security and compliance protocols.
Assigning risk values to entitlements and roles can be a complex process, but it is essential to consider the client’s needs and preferences when implementing these systems in. To know more about these, get with SailPoint Classes.
Identity risk scores are used to validate high-risk users, with eight identified as high risk. So, to minimize the risk, learn SailPoint Online. The composite score is generated using the technology algorithm.
SailPoint Technical Training to learn IAM’s automation
In this, tasks are essential in automating processes in applications. They are used to trigger and schedule tasks to automate processes, such as importing identities, importing entitlements, refreshing identities, and performing maintenance tasks.
Tasks are responsible for aggregating identities, maintaining data, and background activities. To create new tasks, log in and go to the “set up task” section.
SailPoint IAM Training gives IT professionals extensive training and hands-on experience in identity and access management to successfully integrate and operate it’s IAM systems.
The account aggregation and activity alert aggregation tasks are essential tools for managing and analyzing data in real-time projects.
In this scenario, 99% developers will create SailPoint a custom task or rule workflow by copying data from an existing stack and making changes. They will then create a refresh identity cube for which will be placed under the task definition.
By participating in the SailPoint development training, developers will acquire the essential competencies required to effectively integrate and personalize access management and identity governance solutions in enterprise settings. Get access to know how to learn SailPoint.
SailPoint Fundamentals Training
Learn SailPoint identityiq and know how to schedule one more task with a different name, description, and execution frequency. We can also choose whether the task should be executed on a daily, hourly, weekly, or monthly basis, or only once.
It emphasizes to SailPoint identityiq and the importance of monitoring tasks in a system, including scheduling sequential tasks, managing alerts, and preparing reports based on these metrics. Know more on this with SailPoint IIQ Basic Training
To schedule this in account aggregation, group aggregation, refresh, identity, task buffer, maintenance, and certification tasks, we can create sequential tasks, run-rule tasks, and export objects from one environment to another. The plugin covers import and export tasks and can be used for deployment.
Learn SailPoint development at the best.
With SailPoint Training YouTube, you will learn how to create a new task in a system. Standard properties are applied to all functions based on requirements. These properties include the name and description, which can be customized based on the requirement.

Allow concurrency allows the same task to run in parallel with other tasks, allowing it to execute multiple times. Users can add recipients, groups, or specific people’s names to modify the email template.
The email will be triggered when the task ends with failure or failure and will be sent accordingly. This feature is helpful for task monitoring, as it allows for easy tracking and updating of the status of each execution.
SailPoint Advanced Training helps you know policies and processes.
Some of the basic concepts are easily grasped through SailPoint Training Free. Then there are advanced concepts that require Training, for which you need to Enroll. So, SailPoint Training Cost will vary based on the modules you need to learn.
Policies are essential for companies to ensure employees follow the same rules and regulations. They can be defined in various ways, such as role SOD policies, which are designed to restrict user access based on roles and entitlements.
By setting up policies and providing role names, companies can create effective SOD policies that restrict user access and ensure a smooth workflow for their employees.
This outlines the process of creating and managing policies in an organization. Best Online SailPoint Training covers various aspects such as policy name, owner, violation formatting rule, and workflows.

Sailpoint Online Training

SailPoint Provisioning Training
The creation of a role called SOD policy, which allows for the addition of multiple policy rules. Free SailPoint training helps you learn the purpose of creating an entitlement SOD to prevent users from having access to conflicting roles.
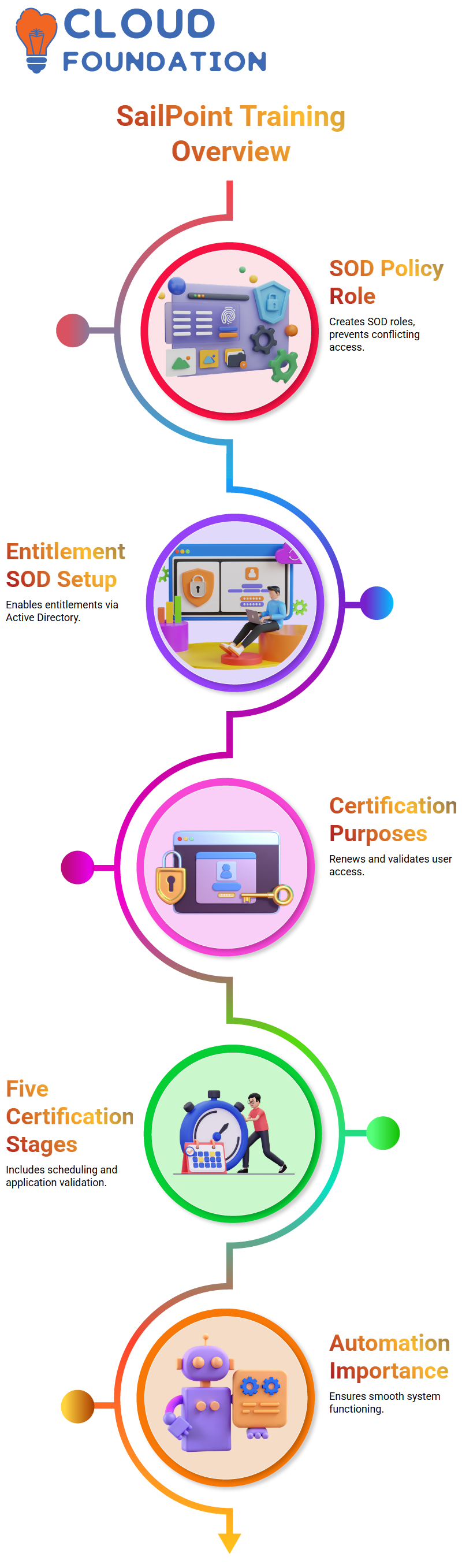
The organization then creates an entitlement SOD related to entitlements, naming them as entitlement SOD. The policy must be enabled active, and the first entitlement set is created using the Active Directory application.
SailPoint Certification Course
Certifications are used to renew and validate access in various systems for audit purposes, ensuring users have the proper access and renewing access, if necessary, in the banking client banking environment. Certifications can be manually validated from one identity to another.
In the SailPoint Certification Course, you can learn about SailPoint certifications, which have five stages that can be enabled or disabled. These stages include
• Scheduling
• Pre-validation
• Scheduling
• Execution frequency
• Application validation
SailPoint training courses offer a comprehensive suite of features for managing certifications, including scheduling, pre-validation, and application validation training. By turning these stages on or off, users can ensure their certifications are valid and meet their needs in SailPoint training classes.
SailPoint Certification Training
Certification is the purpose of user validation, ensuring that users have the proper access and are required to do so. Users can approve or revoke access as part of the validation process. When a certification is triggered in best SailPoint Training, all identities and related entitlements will be populated.
The importance of automation in deployment processes, particularly in the context of certification. They also mention the need for regular updates and maintenance tasks to ensure the smooth functioning of the end-to-end system.
Learn SailPoint and Security Locks
Know about the different types of locks in SailPoint identity training online, including system prop, systemoutprintl, lock debug, lock error, and lock info. Lockall is used for printing everything, while locktrace is used for fine-grain diagnostic information. Developers prefer Lockerror as it deals with errors and changes in code.
In SailPoint online training free, the Apache Tomcat folder contains various lock files, including default ones like Tomcat, Tomcat standard out, standard error, and Catalina file.
These files can be customized based on the user’s requirements. For example, if a custom rule or workflow is created in SailPoint iiq training, the Tomcat standard out file will always display all locks, and this training will let you know about it keenly.
SailPoint Identityiq Free Training
Provisioning is a crucial process for end-users to access their systems. It involves multiple workflows, including identity request initialization, approval, provision, notification, and finalization, all essential for maintaining secure and efficient access to the target system.
The SailPoint IDN Training request initializes the workflow, compiles the provisioning plan into a provisioning project, compiles each job, and checks for policy violations.
It creates an approval set for the user’s selected roles or entitlements and tracks the approval decision for the request. It also checks for any policy violations and throws a policy violation if necessary.
The successful execution of SailPoint admin Training facilitated the organization’s proficient administration of user privileges and access within the enterprise’s identity governance system. SailPoint IDN Training will help you to get a grip on understanding about provisioning,
SailPoint Securityiq Training
The SailPoint online course includes classes on identity and access management solutions that automate the process, so creating a custom workflow is necessary for the back end. This helps you learn how to prepare a workflow to create the account automatically, eliminating the need for manual creation.
Provisioning creates an account in an application, not just an end directory. Creating a custom provisioning policy or rule is optional, as it is already present in the LCM. The provisioning process is universal and does not require any custom workflow.
SailPoint Functional Training on LCM
Provisioning is a crucial process in LCM (Localized Content Management) that involves submitting access requests or certifications and subsequent management of access addition or removal. The process involves five sub-workflows: identity request initialization, approval, provisioning, notification, and finalization.
The main workflow LCM provisioning includes all five sub-workflows, each with its variable. Variables can be used to change the provisioning plan, such as approval schema or approval mode, or to control activities related to policy violations.
SailPoint Basic Training and Policies
Provisioning failures can be managed through various tools and configurations, including the Administrator Console, which provides detailed information on events, lifecycle events, JML-JOIN, MOVIE, and LCM policy violations.
An identity object is created from the identity class, which captures details from the debug page. The log dot error is added to ensure that the identity is populating in the HR application. It also adds a log error to check if the identity object and its attribute are inactive, allowing for the provision of AD access based on certain conditions.
SailPoint Developer Tutorial on Directories
Enabling native change detection in an Active Directory application prevents events and ensures security. By implementing these steps, SailPoint online training cost can vary based on modules and know how to take action on any changes made to the target system and ensure the safety and security of the application.
In SailPoint Classroom Training, you will also learn that only some activities require approvals, and it is rare to have a workflow that does the activity on its own and bypasses the approval process.
The out-of-the-box workflow is the best option for managing native change detection in an organization.
The workflow allows users to bypass Active Directory by adding conditions. This approach ensures users can access the necessary information without logging in individually.
SailPoint Architect Training on Servers
The deployment process involves:
• Logging in to all four servers.
• Ensuring the dataprotection team takes care of the backup.
• Stopping Tomcat services on all servers.
This process is essential for maintaining the system’s integrity and ensuring smooth operations.
The installation requires a thorough backup of all WAR files, replacement of the WAR file, and various tools and capabilities to ensure smooth and efficient deployment.
SailPoint Administrator Training on Capabilities
The discussion focuses on capabilities such as adding locks, SSD, debugging, and troubleshooting lifecycle events. If lifecycle events are not triggered, it is crucial to check if the event is active or inactive, enable locks and logs, and consider using a manager certification manager on the sales point.
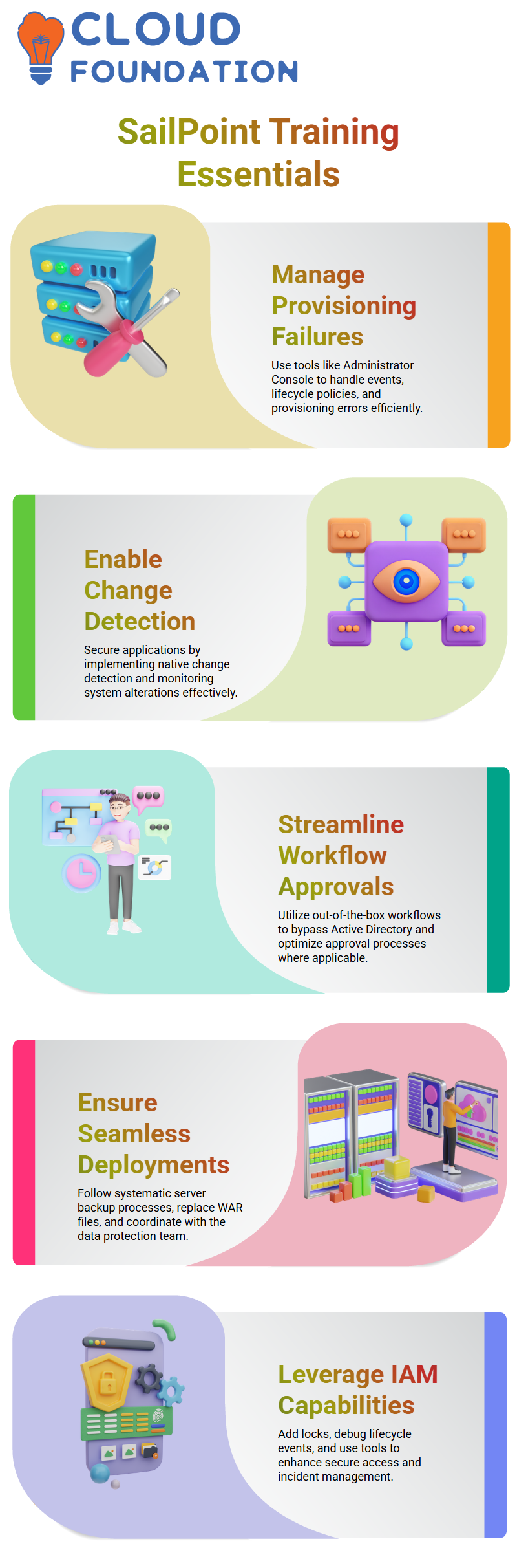
It is an automation tool that allows for easy access to unified portals. It was previously used for triggering incident tickets in the HPS and HP service manager tools. Capability is one of the capabilities that allows users to control their access to specific areas within the platform.
So, with the help of SailPoint training and placement, you will learn about the advanced capabilities of the vast IAM tool.
Sailpoint Course Price


Harika
Author