Network Security Tutorial
Introduction to Network Security
Network security is an integral aspect of cybersecurity that ensures the integrity and safety of a company’s infrastructure by blocking unauthorised entries into networks as well as spreading malware through them.
Goal of data security measures is to protect privacy and accessibility of network. Each company or organisation dealing with large quantities of information must have comprehensive plans in place against various cyber threats.
Password protection is one of the foundations of network security and must be implemented on both personal and professional networks alike.
Workstations can be protected against hazards like hazardous spills thanks to network security. Furthermore, this safeguard ensures data shared over networks by splitting it up into distinct pieces that travel on distinct paths.
Network security infrastructure offers multiple layers of defense against man-in-the-middle attacks and similar risks, providing safeguards to protect users against situations like eavesdropping.
Types of Network Security
Organisations must invest in network security measures in order to preserve both their financial status and reputation, with physical, technical and administrative forms of network protection all playing an essential role.
Physical security is the foundational level, protecting data and networks from unauthorised personnel while assuring confidentiality, and controlling access to external peripherals and routing devices. Small businesses with limited resources must dedicate some of their budget toward security measures.
Technical network security aims at safeguarding information stored or transmitted within or across networks. Transitions within this process serve two roles, as protection from unauthorised users as well as blocking malicious actions by cyber attackers.
Administrative network security ensures data stored or transmitted over a network remains protected and inaccessible to unauthorised access.
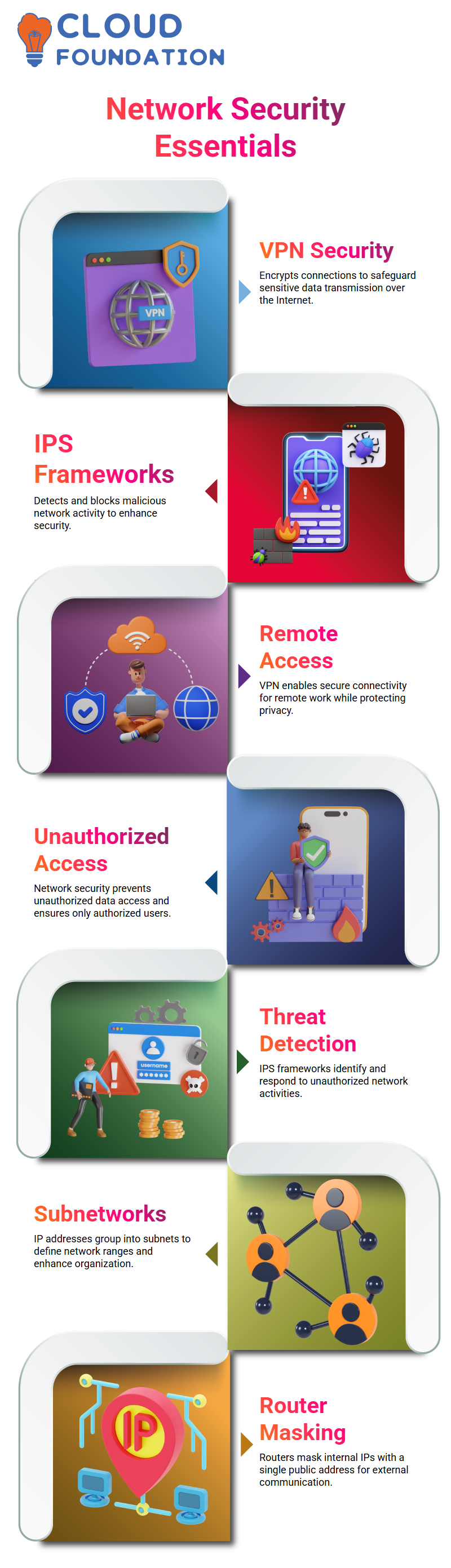
Enhancing Network Security: The Role of VPNs and IPS Frameworks
A virtual private network (VPN) provides secure data transmission over the internet between two devices connected through an encrypted link, providing safe transmission of sensitive material over it.
VPN technology has become an indispensable element of both corporate and personal networks alike, providing critical protection of sensitive information. Prevention systems within network security like an IPS Framework monitor networks constantly for malicious activity to identify them quickly when they arise and take appropriate measures when necessary to mitigate potential breaches in network integrity.
Utilizing hardware or software systems designed to block malicious activity is becoming more and more important in corporate networks and personal networks alike, providing added protection of both devices and networks alike. Implementing VPN technology into both can ensure greater protection.
VPN technology has become ubiquitous within both corporate and personal networks, enabling remote working while protecting online privacy.
Network security should also include inclusion, as it prevents unauthorised access to sensitive data and ensures only authorized individuals may gain entry to the network.
Additionally, Intrusion Protection System Frameworks offer an essential solution for network security concerns by detecting and responding to unauthorised activity on networks. Security threats require a multifaceted and holistic strategy in order to remain protected.
By understanding the fundamental concepts governing network security as well as available tools to implement them, organisations can better safeguard their networks and foster an online environment free of threats and vulnerabilities.
Network Components Overview
Network is defined as any collection of IP addresses which form part of an identified range.
Subnetworks or subnets of IP addresses help define the overall range of local area networks; for instance, all of the IP addresses displayed today on your screen belong to one with IP address 255.255.0.0 as its subnet ID.
The first two flags do not specify values which must appear for all IP addresses on devices in this network, instead they differentiate among multiple IP addresses in it. A router and switch provide this function.
Wide area networks function at their core as an amalgamation of local and area networks that interact amongst themselves and each other.
Data networks, with the Internet as its largest and most renowned example, comprise an interconnection of networks that enable information flow among them. When communicating with devices outside a local network via routers or bridges, routers often hide all their locally allocated IP addresses by allocating one public IP address instead.
Difference between router and switch in a network. A router typically uses only public IP addresses when communicating with devices outside its local network.
Assuring all devices can access a local area network is of vital importance in maintaining network stability.
Understanding IP Addressing and Network Management
A network is composed of devices connected in close proximity that enable communication and the exchange of data among them.
IP (Internet Protocol) addresses are used to distinguish devices connected to networks using the internet; an IP address is an alphanumeric string assigned to any computer connected via this communications medium and represents its digital equivalent of your house or workplace.
Addresses are divided into four sections separated by drops, with traditional trees representing numbers and portions representing 8-bit binary integers.
These integers can be represented using standard decimal notation with dots between each integer value. Computers primarily work with binary numbers composed of zeroes and ones. Each number in an IPv4 address represents an 8-bit binary integer between 0-255.
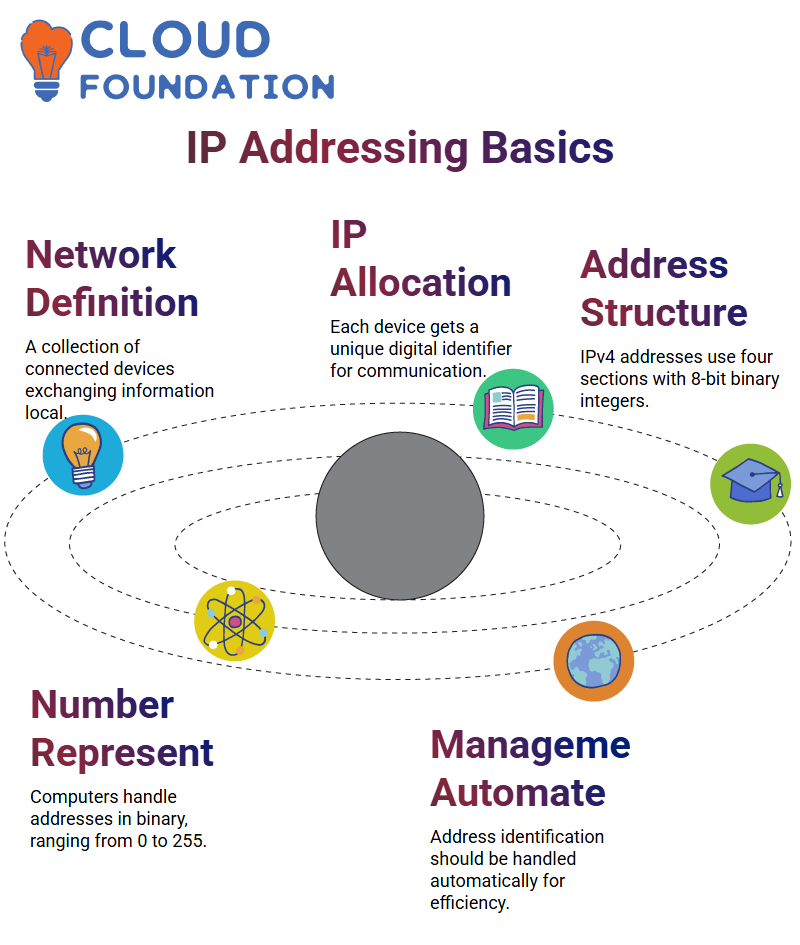
IP addresses aren’t just restricted to devices within one local area network (LAN); each device receives its own IP address from its network administrator.
Each device on a network will have an IP address assigned by its network administrator; this allows for identification by device through their designated address.
Networking serves to connect devices together so they can exchange information. IP addresses only fulfil half this role; therefore they should be managed automatically on devices as part of allotment procedures.
IP Address Classes: Efficient Network Communication
IP Address Classes to Foster Effective Network Communication IP addresses play a pivotal role in network communications systems, helping identify and assign addresses for network hosts.
Network ID, also referred to as host ID, is the first component of an IPv4 address and serves as the keystone reference point when looking at IPv6 addresses as reference for Identification Regions (IR).
IP classes were developed to enable an easy and efficient assignment of IP addresses to network hosts. There are five classes within a network; A, B, C and E represent these IP classes respectively.
Class A caters for large networks where all network host addresses have zero first bits in their octet addresses – ideal for accommodating networks where host names vary significantly across hosts and classes are assigned on that basis alone.
Class B can meet these three requirements by setting its lead bit between 1 and 0; Class C enables IP addresses for low numbers of network hosts by setting its first three bits between one and zero; this range can span 192-223.
Class D multicasting uses multiple signals simultaneously from one host. When used for video streaming, for instance, its lead bit should contain 1s and 0s with network ID range from 224-239s.
Class E IP bits are reserved exclusively for research use and must remain unallocated during an audit process.
IPv4 Vs IPv6
IPv4 addresses provide services tailored specifically for each network’s requirements; additionally they enable stateful or stateless address configuration through either using DHCP server settings for network settings or autoconfiguration settings.
IPv6 addresses also allow hosts and networks to make the switch according to their individual needs, though one primary difference between IPv4 and IPv6 addressing schemes lies in their respective address sizes.
IPv4 addresses consist of 32-bit addresses and constitute the fourth version of Internet Protocol, while IPv6 utilizes 128-bit addresses as its latest implementation of it.
The second difference lies within their respective address fields. IPv6 addresses use numeric data consisting of four fields separated by periods; bearers for IPv6 are composed of alphanumeric fields separated by colons.
Address configuration relies on addresses, while network setting complies with system requirements. IPv6 also supports automatic configuration settings to optimize system efficiency.
Each IP contains its own set of R gasses which may differ.
IPv4 addresses number approximately four billion; in contrast, there are 2128 addresses allocated under IPv6.
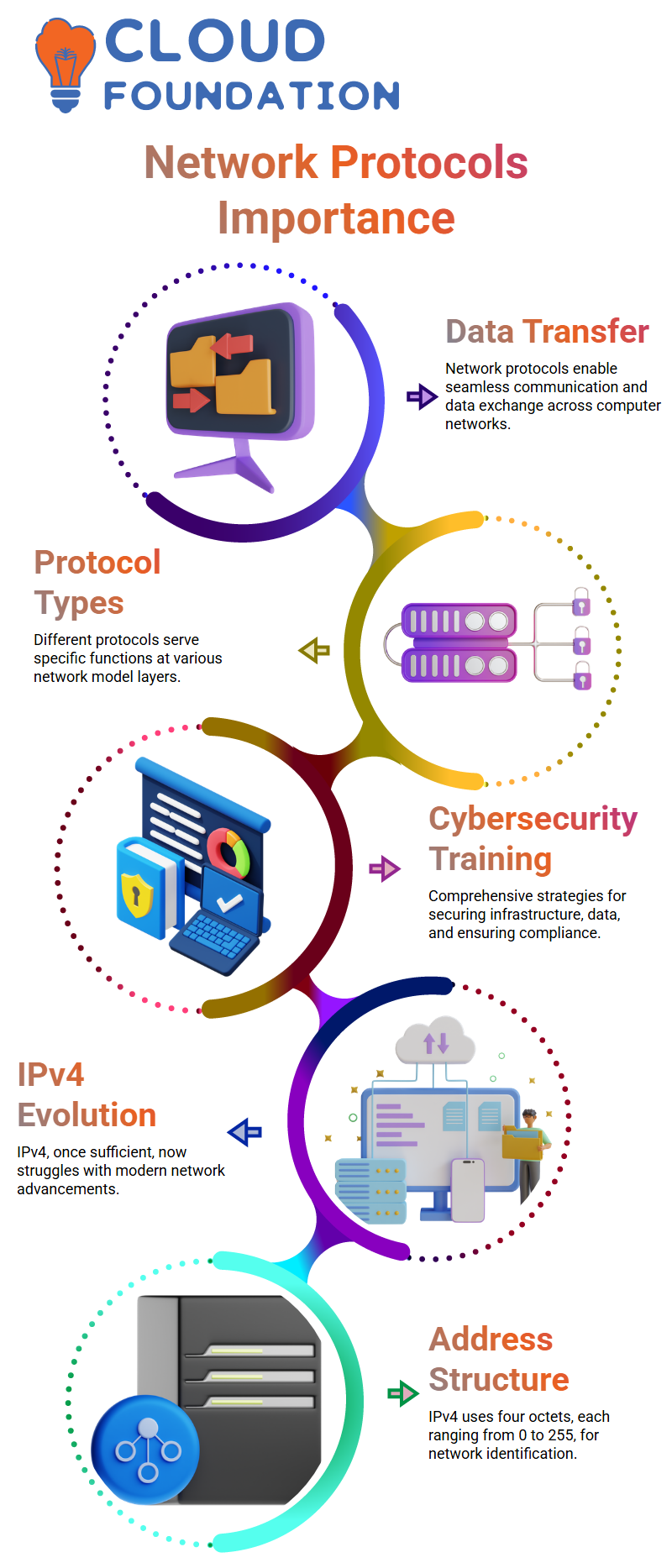
Importance of communication and implementing various network protocols
Network protocols play a vital role in providing communication and data transfer among various computer networks.
This paper introduces several types of network protocols, each tailored for specific tasks at specific layers in a network model.
The post-gadget program presents an all-inclusive strategy for mastering cybersecurity, covering measures that protect infrastructure and secure data, in addition to employing mitigating techniques and compliance practices.
This program offers various certification courses as a foundation of training to empower individuals to thrive in an ever-evolving realm of cybersecurity.
Security continues to evolve rapidly with IPv4 addresses being initially sufficient during initial network requirements but now inadequate due to advancements in network technology.
IPv4 addresses range between 0-255 in decimal notation. They feature four octets separated by periods to represent their network ID – this unique address of your network.
Understanding the significance of 32 bits total IP addresses in IPv4 format was adequate during early phases of network usage but is currently insufficient due to advances in network technology. IPv4 addresses consist of four octets separated by periods and used for storage and transmission across the internet.
Securing Networks: NAT and Firewall Protection
NAT stands for Network Address Translation; this technique converts one IP address into another when packets travel through a router.
This process enhances security while simultaneously decreasing IP addresses required by an enterprise. A router receives specific information which must then be transmitted to local devices in their network for verification before further transmission occurs.
Internal routing tables identify the proper internal IP addresses and destinations to send external data, but if an outside device attempts to directly communicate with one on the local network it could pose a security threat.
Secure environments can reduce this risk through implementation of M3 and creating and monitoring exit rules. A firewall is a type of network security device which analyzes incoming and outgoing network traffic to allow or deny data packets depending on pre-established security rules.
Firewalls serve a crucial purpose: they create an interstitial barrier between local networks and external traffic sources such as the internet. Most commonly seen is packet filtering firewall, which inspects packets to block transmission before transmitting.
Filtering firewalls check packets and deny passage if they do not adhere to predetermined standards, making sure only compliant packets pass.
Also, they examine packet’s destination and source IP addresses to make sure that packets comply with an acceptable rule on the firewall.
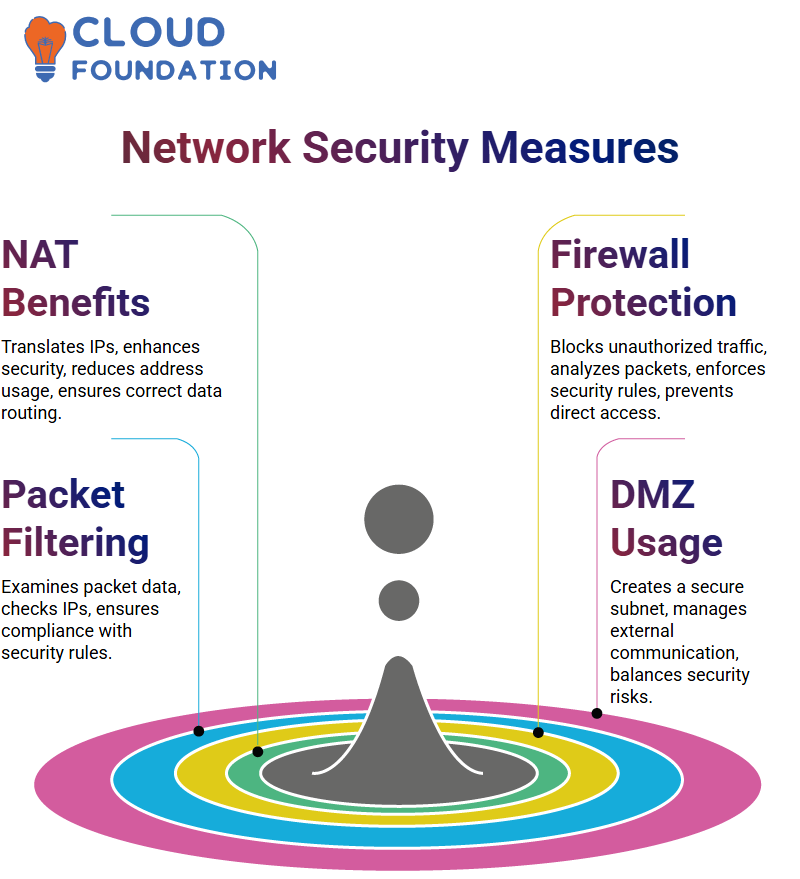
Firewall Rules: DMZ and Port Forwarding
A firewall plays an essential role in allowing external requests from reach individual computers or devices on local networks.
There are two approaches available to facilitate this: behavior and forwarding. Behavior uses a demilitarized zone (DMZ) for direct communications with local network devices.
Forwarding is also used to enable external devices access private networks by translating an external IP address and port into internal IP addresses and ports.
Step one of this process entails creating a DMC subnet consisting only of devices required by external requirements, then when data arrives it passes onto DNG subnet and onto all other devices via routers.
However, since any external information could access devices on a network without going through firewall checks first, this method poses serious security concerns.
Port forwarding is another means of providing external access to private networks by mapping an IP address and port from external IPs/ports into those on internal IP addresses/ports.
Devices interact, with a network gateway using IP addresses to grant access to private networks. Addresses and ports allow communication among devices while TCP IP is used for basic internet usage.
Port 80 is used on every network and extra files or rules can be created to open specific ports to external devices for communicating purposes.
Network sniffing tools
Network sniffing tools (also referred to as packet sniffers or intelligent network sniffing tools) are software applications used for monitoring and analyzing network traffic including packets. Popular tools in this regard include Packet Sniffer.
These tools specialize in analysing protocol data, packets transmitted across networks and packet sniffers – tools designed specifically to detect and analyse packets during their transmission over networks.
Different color combinations are employed to represent various packets and protocols used for troubleshooting various network issues.
Engineers can test software vulnerabilities or network devices susceptible to attacks and check for malicious or hacking activity on the network. Furthermore, engineers can examine potential security flaws that exist across networks that they manage or maintain.
Performance of Packet Sniffer is another critical consideration when using network sniffing tools, since its efficiency depends on your unique requirements for software like this one. Packet Sniffer may serve well for detecting and analysing packets.
Performance monitoring is another essential element to keep in mind when using a network sniffing tool. Engineers can utilize its software to test whether software or network devices are vulnerable to attacks; additionally it may reveal malicious activity on the network as well.
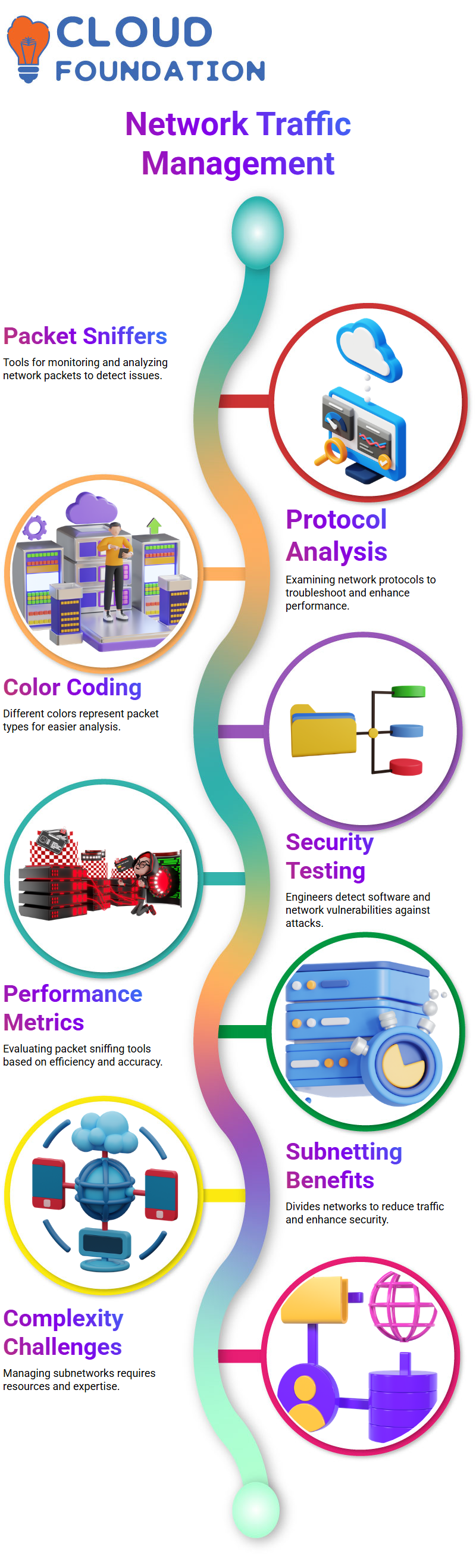
Subnetting tool for managing network traffic and ensuring network security
Subnetting provides an effective tool for controlling network traffic and assuring network security, by sharing data among specific areas rather than broadcasting to all.
This method helps avoid unnecessary traffic in a channel and ensures only two hosts can receive specific data at one time. A router then sends that data only to specific portions of a subnetwork, thus saving resources by not utilising all network channels at the same time.
Subnetting has many other advantages as well, such as increased network security. Subnetting protects against hacker attempts made on networks due to complex subnetworks preventing any attempts made at intrusion into them.
By targeting one or two subnetworks, an attacker may be able to bypass all others and attack only certain networks – though using subnetting may bring other problems as well.
Subnetting increases complexity and expense in its administration and maintenance processes, necessitating more resources to effectively oversee this network, potentially taking longer than originally estimated and incurring greater time costs in managing it. Furthermore, their complexity poses difficulties to identify threats to prevent attacks against their subnetworks.
Troubleshooting network connectivity and routing issues using commands
The CLS command, used for performing multiple searches to discover both domain name and IP address information about networks, while nslookup can help troubleshoot network connectivity by finding its IP address.
Traceroute is used to troubleshoot routing issues by displaying its routing table.
Communication occurs between IP addresses and Mac or physical addresses in systems. A fourth command, Path Ping, combines Traceroute with Ping commands in order to display detailed output for up to 30 hops in your network.
The ARP command shows communication exchanged between an IP address and system’s physical or MAC address. ARP uses this functionality in order to display this exchange of communication data between IP and system MAC or physical addresses.
Path Ping combines Traceroute and Ping commands for more in-depth network information for up to 30 hops within any network.
TCP ModelLayers and Functions
Layers and Functions The model comprises four separate layers – application layer, transport layer, internet layer and network access layer – wherein each acts as an interface to other programs that require communication via TCP model. In particular, application layer functions as the link between application programs using it and programs using it as communication mediums.
Data representation, transmitting to users, and forwarding to transport layer are some of its duties.
Transport layer divides application-generated packets into sequences before transporting them directly to their destinations devices is performed at this layer.
The destination device is responsible for error-free data transmission and controlling its flow rate, while its counterpart, Internet Layer 1, is accountable for transmitting it over its respective network by providing channels and routes where packets may travel safely over its path of transport.
The updated model encompasses application, transport, Internet Protocol (IP) and data link layers – each one performing distinct duties and using its own protocols and tasks.
Communication channels play a pivotal role in transmitting data over the internet. They comprise networks connecting devices via different protocols – including IPv4/ARPv6, Data Link Layer Layer etc – in order to ensure efficient data exchange.
TCP model is an essential feature that assigns IP addresses for every system on a network channel.
TCP provides users and systems access to various data formats over communication channels. In doing so, these systems can easily identify themselves on the internet and access various types of files.
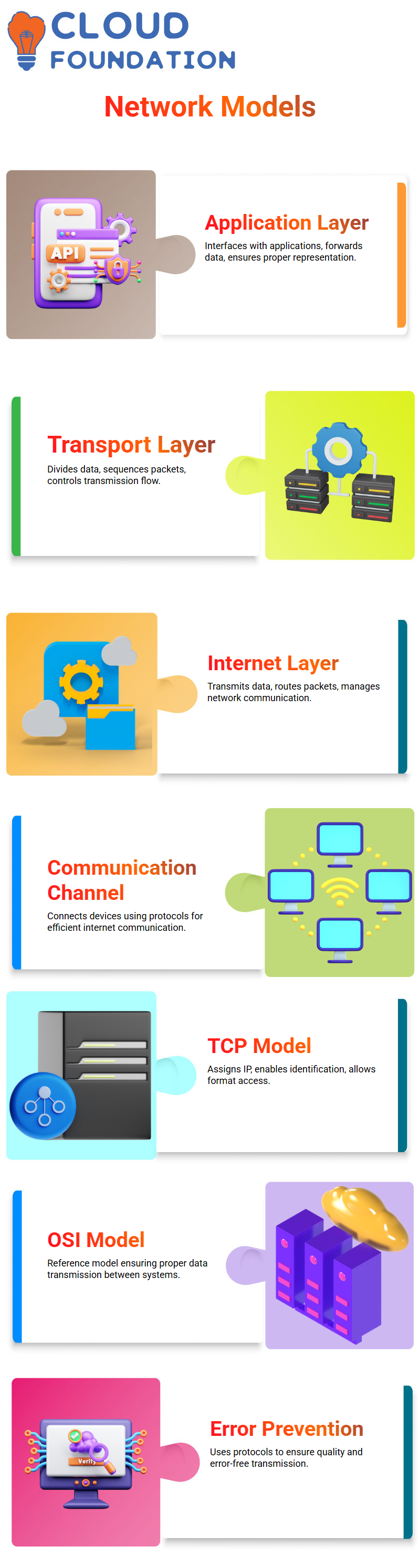
OSI Model Layers and Functions
The Open System Interconnection (OSI) Model plays an essential part in network communication, serving as the model of reference for network channels. It is most frequently employed when exchanging information between two computers with different operating systems installed.
Data are shared over communication channels, but errors often arise due to different operating systems installed or transmission network problems during transmission.
To address these concerns, the OSI model (which consists of seven layers) can help. Each layer employs its own set of protocols when transmitting data over network channels.
These protocols aim to facilitate accurate modeling and conversion of data for transmission over network channels.
OSI model employs a seven-layer structure consisting of distinct functions and protocols at every layer to protect data quality and ensure its continuity.
These functions and protocols are applied at various layers to safeguard data when transmitted over communication channels, thus creating error-free transmission over them. The OSI model was specifically created with this in mind.
Attaining this goal involves employing a set of protocols and standards which govern data modeling and conversion for transmission over network channels.
Conclusion
Network security is an integral element of cybersecurity, safeguarding data and infrastructure against unauthorised access and malware threats. It encompasses various strategies and tools – physical, technical and administrative measures – used to secure network environments; technology like VPNs, IPS frameworks and firewalls plays an essential role in combatting potential cyberthreats.
Alongside security measures, understanding key network components like IP addressing, protocols, and management tools is vital in order to guarantee safe communication across devices and systems. IPv4 to IPv6 transition demonstrates this need as networks expand. Furthermore, techniques like subnetting increase security by isolating parts of a network from potential attacks by isolating parts from each other thereby decreasing attack risks across networks.
Effective network management also relies on troubleshooting tools and protocols like ARP, ping and traceroute for effective connectivity and routing issues resolution. Finally, OSI and TCP models form the backbone for data transmission across diverse systems providing standardised communications protocols across each one.

Sai Susmitha
Author